Secure chat systems
Optimising back channel interjections into other people’s meetings
February 15, 2015 — April 21, 2023
tl;dr Everyone use Signal and/or Keybase, or just meet up face-to-face. In a Faraday cage.
The Electronic Frontier Foundation reviews good encryption options, and comparitech has one focused on chat apps specifically.
The ephemeral nature of chats is possibly easier to practically secure than email, at least if you do it right.
There are too many chat programs which aspire to security and not enough secure anything else, and we can’t persuade people to use even the secure chat clients, let alone the same chat protocols. Building them is hard and many are doing it badly. The ones that exist are often awful — gossip is that the stalwart pidgin/adium/libpurple is bad in that it is full of security bugs. Even without that, the underlying protocol (XMPP) by design leaks information about your contact list to the server. A more modern approach is Off-The-Record chat which is available in some systems, but implemented with varying degrees of laxity. For a visualisation of how the popularity of chat clients increases roughly in proportion to how much of your information is given to unaccountable third parties, see the (now somewhat dated) EFF chat scorecard.
Skype is particularly egregious. It is an NSA honeypot, and not even an especially usable one.
There are attempts to do it right below as regards confidentiality, but consider also the problem of jurisdiction. Trumping end to end encryption shows one way that secure confidential communication is being white-anted in various states. Indeed, this has been partly outsourced to my own nation, Australia via the AssAccessBill.
1 UX
You know, I should think about that. Chat with glue explores UIs in chat-based interfaces.
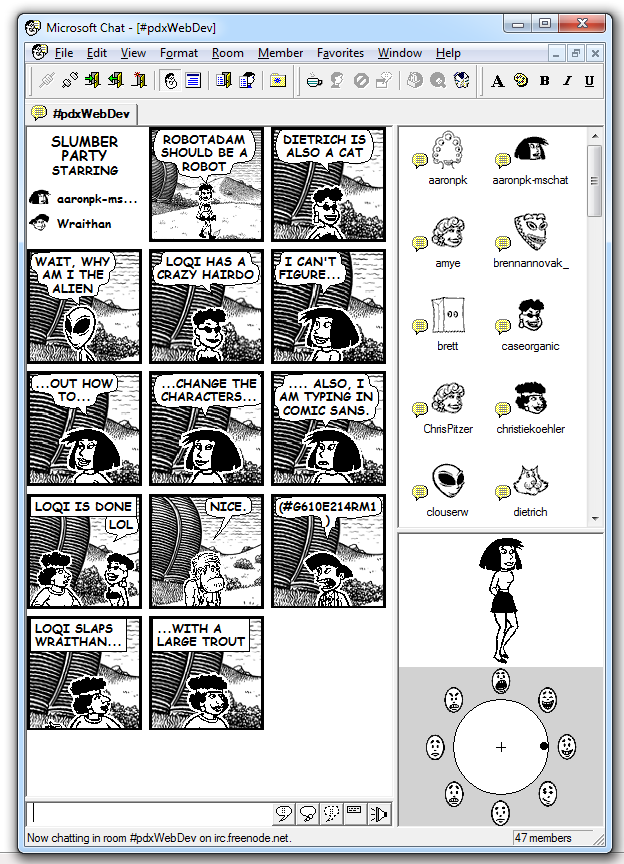
Robert Fabricant mentions a defunct product, comic chat
2 Does Apple push notification destroy encrypted messenger privacy?
I am no expert but it sounds like they may be implemented in a mostly secure way, insofar as you trust the device at all.
3 Services
3.1 Signal
Signal (Formerly redphone):
Free, worldwide, encrypted voice calls for iPhone and Android by Open Whisper Systems. Does not disclose message content, in principle. Does not disclose contact list, if they are to be believed.
Signal uses your existing number, doesn’t require a password, and leverages privacy-preserving contact discovery to immediately display which of your contacts are reachable with Signal. Under the hood, it uses ZRTP, a well-tested protocol for secure voice communication.
Signal was designed specifically for mobile devices, using a jitter buffer tuned to the characteristics of mobile networks, and using push notifications to preserve battery life while still remaining responsive. Signal is also Free and Open Source Software, allowing anyone to audit the code for correctness or help contribute improvements. The project even pays out a percentage of donated Bitcoin for every merged pull request.
Seems good that it is semi-open, friendly, widely used etc. Not as polished, reliable or easy as more mainstream clients.
The Signal algorithm is apparently used in iMessage and Whatsapp, although how can you tell in these secretive closed-source apps? Whatsapp, at least, breaks the security of the protocol in aid of convenience, and uploads your contacts to suspect 3rd parties.
Signal is what I’m recommending not because it is perfect, but because it is widely used, and OK-ish. The governance could be better, but most others are worse. For some ideas of the governance controversies, see jwz: Signal hops on the Dunning-Krugerrand bandwagon, Et tu, Signal? on Signal’s brief foray into cryptocurrency.
FWIW cryptocurrency looks to me reasonably aligned to the values of privacy chat and worth trying at least. Unlike many uses of cryptocurrencies that I see pitched, which do not look worth trying because they are stupid.
There is an alternative Signal client called Axolotl.chat. It promises alternative features such as an additional layer of encryption and accounts without phones.
3.2 Exporting
One problem is that it’s hard to archive chat history. You can export from Signal Desktop via a tedious manual process. See some wrinkles are discussed here.
There is an automated version via SCAB, although NB the code linked there does not work. I did better with one of the github forks —this one seems OK. In addition to the instructions there, it is possibly also worth manually installing pysqlcipher3. Hair-raising hacks such as faking gcc-5 installation are required for that:
NB: these methods reveal that the messages are not really encrypted on the desktop app. Be careful. Is your hard drive encrypted? Is it encrypted enough for you to rely upon it.
4 Session
Session is a Signal-workalike alternative backed by IP anonymisation incentivised by a cryptocurrency called $OXEN.
- Faq - Oxen | Privacy made simple.
- Session App Review: Everything You Need to Know
- Session | Send Messages, Not Metadata. | Private Messenger
- Oxen
4.1 Keybase
keybase is neat. It’s a chat(+other things) program for your mobile or desktop, which connects you with your social profiles, e.g. twitter or github or website or whatever. Friendly, easy to use. keybase.io/danmackinlay.
The edges are still rough (e.g. high CPU demand for the desktop client). I’m not sure exactly how secure it is. Worth investigating though.
It has fallen out of favour since being bought by zoom.
4.2 Telegram
Mobile: Telegram is popular in Germany, but has possibly shitty security. Probably better than nothing, or if you have lots of German friends.
4.3 Matrix
Matrix is some kind of messaging layer for the internet, at lower level than a chat solution per se. Specifically, it aims to
[provide] an open universal communication layer perfect for VR calling, messaging and collaboration, powering immersive experiences for conferencing, tourism, entertainment, telepresence, e-learning, etc. […] Matrix is that missing signalling layer for WebRTC. If you are building VoIP into your app, or want to expose your existing VoIP app to a wider audience, building on Matrix’s SDKs and bridges should be a no-brainer.
En-to-end encryption is available but optional. The recent security breach is, amongst other things, a lesson in why you should not trust server encryption - all the server-encrypted stuff was compromised despite their care in maintaining the servers themselves, but end-to-end encrypted messages appear to have been safe.
- Element is the flagship group-oriented chat system for Matrix. Looks a little like Slack.
- tchat is a French government-backed (?) fork (?)… installation ? something.
- mozilla uses this to power its internal discussions
If you want to run your own infrastructure to make this go you need to run a server. The current reference server is called synapse. There is a server rewrite called dentrite which claims to be less hacky/more scaleable/less tested. There are docker versions.
As for how much server space to provision?
The homeserver stores all \[clients’\] personal chat history and user account information - much as a mail client connects through to an IMAP/SMTP server. Just like email, you can either run your own Matrix homeserver and control and own your own communications and history or use one hosted by someone else (e.g. matrix.org) - there is no single point of control or mandatory service provider in Matrix, unlike WhatsApp, Facebook, Hangouts, etc.
So if you are hosting some geeky users this will get quite large, storage-wise.
4.4 Wire
Like Signal but with a better jurisdiction?
A free, personal account gives everyone the benefits of a secure, privacy-focused messaging app. Personal accounts can connect and communicate with Pro accounts.
- Messages, calls, photos and files — end-to-end encrypted
- Beautiful apps for mobile, desktop and web
- No phone number required to register
- No ads, no profiling, no user data sold to anyone
- Swiss jurisdiction, servers in Germany and Ireland
4.5 Jami
Desktop, mobile. Jami I think formerly GNU Ring.
The application uses distributed hash tables (DHT) to establish communications. This technology eliminates the use of centralized registers (servers) and the retention of personal data. Jami is based on a distributed network technology, eliminating the need for servers. Mass surveillance can not be undertaken by the servers as there is not any.
Jami stores your secrets (private keys for encryption and identity) only on the device which executes it, which belongs to you. Your device is therefore the sole holder of your information.
Jami offers a digital identity with accounts that do not require anyone exposing their personal identity. All of the communications are encrypted with no exception with the most advanced current techniques. As free software, Jami is underpinned by an essential objective: to be a distributed communication system that respects the privacy of its users, thanks to its design without infrastructures or centralized servers.
4.6 quest messenger
qDesk Messages is on track to become the first fully featured, cross-platform, publicly auditable, decentralized, real-time, dag based end-to-end encrypted messenger with a feature to exchange goods and services and send payments.
In this module you can create end-to-end encrypted channels, organize them in folders, share the folder structure with your invite, control the channels you own, participate in self-owned channels. Have private conversations or public channel discussions. Use Audio/Video in 0.9.5+ for groups or private conversations. Ban and report users in 0.9.5+. Alias and profile picture are linked from qD Social. Peers can nickname participants and override the information that references other peers social profiles.
We are planning the integration of other messaging protocols like Matrix and IRC.
4.7 Meta-chat: Matterbridge
Matterbridge is product spun off from Mattermost chat, providing a
bridge between mattermost, IRC, gitter, xmpp, slack, discord, telegram, rocket.chat, steam, twitch, ssh-chat, zulip, whatsapp, keybase, matrix and more with REST API (mattermost not required!)
Looks neat. I do not cover the Mattermost product itself that spawned this matterbridge thingy, since mattermost is low security and indeed using this bridge likely implies unfortunate infosec weaknesses. But so handy! So shiny! even allows, e.g. bridging facebook messenger to a real app. The WhatsApp basic example illustrates what is going on here.
4.8 Bridgefy chat
The flagship app of the Bridgefy mesh network, about which I know little except that it doesn’t require the internet.
4.9 Wickr
Mobile: Wickr is not open source but looks interesting because it has trendy cryptographers backing it. Claims not to disclose message content or your contact list, much like Signal.
🏗 Update to mention public source disclosure by the company. This is probably more secure now.
4.10 Mumble
Mumble is a free, open source, low latency, high quality voice chat application.
Mumble is primarily intended for gamers, and was the first to establish true low latency voice communication over a decade ago, but finds good use in many different environments as well.
We heard from users who record podcasts with our multi-channel audio recorder, players seeking realism with our positional audio in games, Eve Online players with huge communities of over 100 simultaneous voice participants (I bet they make good use of our extensive permission system 😄), the competitive Team Fortress 2 community making us their required voice communication platform, hobby radio transmission users, and a variety of workplaces adapting Mumble to fit their needs - be it on-head mobile devices or communicating across countries or into airplanes.
Administrators appreciate Mumble for being able to own their and their users data. Some make use of the extensive permission system for complex scenarios (for example separating two groups but leaders being able to talk to both). Some love to provide their users with additional functionality with scripts making use of server APIs, or host music bots and the like that connect to the server. Those that have an existing user database often make use of authenticators to allow authenticating with existing account login data.
4.11 Chat over IMAP
COI Chat-over-IMAP backloads real-time chat into email servers. Unclear if this are capable of forward secrecy. Or if this is actually sane.
4.12 Coyim
CoyIM is a new chat client that is safe and secure by default: no settings to change, no plugins to install, no computer configuration to change.
Not yet audited. Do not use for anything sensitive… CoyIM is a standalone chat client that focuses on safety and security. It is a self-contained program that runs on Windows, Linux and macOS. CoyIM only supports one chat protocol - XMPP (sometimes known as Jabber). CoyIM has carefully picked and chosen the features that are necessary to create a good chat experience, while keeping the attack surface of the system to a minimum.
It also has built-in support for Tor, OTR and TLS. The Tor support allows users to become anonymous while chatting, OTR makes end-to-end encryption of communication possible, and TLS adds another layer of encryption for the communication with chat servers. These features are not plugins or extras in any way.
CoyIM is implemented in Go. Many other implementation languages open up the door for a large number of attacks; we try to minimize those risks by using Go.
Does not leak message content but AFAICT does leak your contact list.
4.13 Tox
Desktop: tox is a chat protocol and implementation
Tox is a free-as-in-freedom, peer-to-peer, end-to-end encrypted, distributed, multimedia messenger. Using existing technologies such as dispersed networking and strong cryptography, Tox can provide a superior instant messaging experience than current market offerings. Files can be shared as fast as you and your partner’s Internet connection allows, audio calls are instantaneous, and there are no arbitrary limits to how many people you can have in a group conversation.
Favoured client seems to be qTox.
You can probably stop reading here; that should be enough chat clients to keep anyone busy and too many for fragmentation of your chat communities. From here on, the suggestions get successively more esoteric and/or untested.
4.14 Mozilla Hello
Desktop: Hello is the new firefox one. How does that work now?
4.15 Cryptocat
Desktop/mobile: Cryptocat is an open implementation of OTR for text chat. TBC
4.17 Chatsecure
iOS: Chatsecure
ChatSecure is a free and open source messaging app that features OMEMO encryption and OTR encryption over XMPP. You can connect to your existing Google accounts or create new accounts on public XMPP servers (including via Tor), or even connect to your own server for extra security.
Unlike other apps that keep you stuck in their walled garden, ChatSecure is fully interoperable with other clients that support OMEMO or OTR and XMPP, such as Conversations (Android), CoyIM (Desktop), and more.
See the suggestive (but old) security audit
4.18 Bitmessage
Desktop: bitmessage
is a P2P communications protocol used to send encrypted messages to another person or to many subscribers. It is decentralized and trustless, meaning that you need-not inherently trust any entities like root certificate authorities. It uses strong authentication which means that the sender of a message cannot be spoofed, and it aims to hide “non-content” data, like the sender and receiver of messages, from passive eavesdroppers like those running warrantless wiretapping programs.
4.19 Jitsi
Desktop: Jitsi is an open-source skype-ish client. Unique feature: multi-person videoconferencing.
4.20 Keet
Keet by Holepunch is a decnet option.
Keet only shares end-to-end encrypted data between participants in your calls. Without middlemen, third-parties, or servers, there’s nobody left who can snoop or leak data.
4.21 Dissent
Group communications are nice to have if you have more than one friend. Dissent is one a open-source attempt to provide that with good academic credentials. No released products, though, and I suspect this project is dead
Dissent’s technical approach differs in two fundamental ways from the traditional relay-based approaches used by systems such as Tor:
Dissent builds on dining cryptographers and verifiable shuffle algorithms to offer provable anonymity guarantees, even in the face of traffic analysis attacks, of the kinds likely to be feasible for authoritarian governments and their state-controlled ISPs…
Dissent seeks to offer accountable anonymity, giving users strong guarantees of anonymity while also protecting online groups or forums from anonymous abuse such as spam, Sybil attacks, and sockpuppetry. Unlike other systems, Dissent can guarantee that each user of an online forum gets exactly one bandwidth share, one vote, or one pseudonym, which other users can block in the event of misbehavior
Dissent offers an anonymous communication substrate intended primarily for applications built on a broadcast communication model: for example, bulletin boards, wikis, auctions, or voting. Users of an online group obtain cryptographic guarantees of sender and receiver anonymity, message integrity, disruption resistance, proportionality, and location hiding.
4.22 Ostel
OStel is a public testbed of the Open Secure Telephony Network (OSTN) project, an effort with the goal of promoting the use of free, open protocols, standards and software, to power end-to-end secure voice communications on mobile devices, as well as with desktop computers. Both are concepts from The Guardian Project.
4.23 Pidgin/Adium etc
Pidgin/adium/libpurple works, for what it is worth, but are probably insecure because of bugs and deprecated and leaks your metadata (citation required). Does not disclose message content if you choose the right settings but does leak, for example, the identities of who you are contacting. Probably if you are using this, you want to use coyim instead?
4.24 Skype if you must
Skype, as we have already mentioned is honeypot spyware, that reads your passwords. But you have some colleagues who are determined to use it, right? You could run it in a docker jail, but it is probably simpler to use the web client.
5 Group chat
You want a social media site but for a single group? Or for a single project?